Just a guy in Vermont trying to connect all the dots...
Author's posts
Sep 11
Tor (The Onion Router) Expands IPv6 Support in 0.2.4.1-alpha
 Last week the Tor Project announced a new alpha release 0.2.4.1 that includes as one of its major features expanded support for IPv6. From the release notes:
Last week the Tor Project announced a new alpha release 0.2.4.1 that includes as one of its major features expanded support for IPv6. From the release notes:
- Bridge authorities now accept IPv6 bridge addresses and include them in network status documents. Implements ticket 5534.
- Clients who set “ClientUseIPv6 1″ may connect to entry nodes over IPv6. Set “ClientPreferIPv6ORPort 1″ to make this even more likelyto happen. Implements ticket 5535.
- All kind of relays, not just bridges, can now advertise an IPv6 OR port. Implements ticket 6362.
- Directory authorities vote on IPv6 OR ports using the new consensus method 14. Implements ticket 6363.
This builds on an earlier 0.2.39 alpha in December 2011 that introduced initial IPv6 support and follows on some plans for IPv6 support written earlier in 2011.
If you are not familiar with the Tor Project it is a widely used tool for protecting your privacy and enabling anonymous use of the Internet without being tracked. The history of Tor is quite interesting because it originated with a desire within the U.S. Navy to protect online government communications but today is used by many people who want to access Internet services without exposing their identity and/or location.
Tor has many uses across a wide range of fields… and now, at least in an early release version, it can work even better across IPv6!
Sep 11
Can You Add 1 Line of HTML To Your Site To Help Measure DNSSEC Usage?
 Can you please help out with efforts to measure the number of DNSSEC-validating DNS resolvers out there?
Can you please help out with efforts to measure the number of DNSSEC-validating DNS resolvers out there?
The folks at Verisign Labs are conducting some research into trying to understand what level of DNSSEC-validating resolvers are out on the open Internet. This is critical to understand as the availability of DNSSEC-validating resolvers is a key piece of getting DNSSEC deployed.
They are asking for your help.
If you operate a website, they are asking if you can please add one line of HTML to your site, preferably in a page header, footer, sidebar or other component that gets frequently loaded:
<a href=”http://prefetch.validatorsearch.verisignlabs.com”></a>
That’s it! As they say on their page:
This HTML snippet should have no visible impact on a rendered page. Since nearly all web browsers now implement DNS prefetching, the code above results in a DNS query for the name shown and allows us to characterize the recursive name server that the query goes through.
They also mention that you can alternatively modify the HEAD element of your page to include this one line of code:
<link rel=”prefetch” href=”http://prefetch.validatorsearch.verisignlabs.com” />
I’ve chosen this latter approach here at Deploy360 and as a result visitors to our site will be helping with this important research. If we can get more sites adding this code, Verisign Labs can get that many more data points feeding in and helping them characterize the level of DNSSEC validating resolvers out there.
Here at Deploy360, we are in favor of research like this because we’d like to get a baseline now and then see trends over time. Encouraging the wider deployment of DNSSEC-validating resolvers by ISPs and other network operators is one of the key activities we are planning to work on over the next 12 months – and this research will help us and many others understand how successful we are collectively in encouraging that deployment.
Can you please help you by adding a line of code to your site? (Thanks!)
P.S. For those curious to learn more about “DNS prefetching” (also called “pre-resolving” by some) and how this research works, here are some articles you may find of interest:
- Chromium Project: DNS Prefetching and related blog post from September 2008
- Mozilla Firefox: Controlling DNS prefetching and an explanation in a blog post
- Microsoft IE: Internet Explorer 9 Network Performance Improvements (“DNS pre-resolution” discussed later in the article)
- Fascinating cautionary tale: “DNS Prefetching Implications” about how the way a site/service was constructed had implications that caused prefetching to incur significant costs for the company.
Sep 10
FIR #668 – 09/10/12 – For Immediate Release
Sep 07
Speaking in Montenegro about DNSSEC on September 12
 On Wednesday of this week I’ll be speaking about DNSSEC at the 5th international conference for ccTLD registries and registrars of CIS, Central and Eastern Europe in Budva, Montenegro. I’m very much looking forward to this event as it is entirely focused around the concerns of registries and registrars – and they are one of the key groups who can accelerate the deployment of DNSSEC. In fact, you can see DNSSEC come up a few times on the agenda – and I’m looking forward to hearing the case study of the .UA deployment of DNSSEC.
On Wednesday of this week I’ll be speaking about DNSSEC at the 5th international conference for ccTLD registries and registrars of CIS, Central and Eastern Europe in Budva, Montenegro. I’m very much looking forward to this event as it is entirely focused around the concerns of registries and registrars – and they are one of the key groups who can accelerate the deployment of DNSSEC. In fact, you can see DNSSEC come up a few times on the agenda – and I’m looking forward to hearing the case study of the .UA deployment of DNSSEC.
My session on Wednesday is titled “Key Steps in Accelerating DNSSEC Deployment” and for the registries and registrars the steps really can be ultimately reduced down to these:
- Registries need to make it as simple as possible for registrars to upload DS (Delegation Signor) records into the registries’ zones.
- Registrars need to make it as simple as possible for DNS hosting providers to upload DS records into the registrars databases.
Those two steps right there would greatly accelerate the deployment of DNSSEC in those ccTLDs.
That’s not all I’ll talk about, of course. I’m also going to be discussing the growth of the .NL signed domains as that example may be something some of the ccTLDs can replicate. I’ll be talking about how the ongoing work with DANE securing SSL/TLS certificates via DNSSEC should spur enterprise interest in deployment. I’ll be providing some examples of a good user experience … and much more. I’ll be making the slides available later and potentially an audio or video recording if I am able to do so.
The main point of my attendance, too, is to interact with registries and registrars and find out what we can do to make it easier for them to deploy DNSSEC. That feedback will certainly help our DNSSEC content roadmap and help us prioritize what materials we are creating first.
If you attending the event I look forward to meeting up with you, and I look forward to learning from those there about DNSSEC – and all the other issues – in the Central and Eastern European region.
Sep 07
New Mailing List for “Migrating Apps to IPv6” Updates
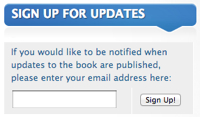 Would you like to be notified when updates are made to “Migrating Applications to IPv6“? If so, there’s a nifty little sign-up box over in the right sidebar that will add you to an email distribution list that I will use ONLY to alert you to news about the book. Info about updates will also be posted here to the book’s blog, of course, and will also appear on the Google+ page and in my normal Twitter stream. But I realized recently that some readers might want to receive specific messages when updates are available. If you purchase the ebook directly from O’Reilly, you’ll get notified through their notification system, but if you purchase through another retailer – or would just like to receive an extra update, please feel free to subscribe. I promise I won’t spam you or do anything else with your email address outside of alert you to the new updates.
Would you like to be notified when updates are made to “Migrating Applications to IPv6“? If so, there’s a nifty little sign-up box over in the right sidebar that will add you to an email distribution list that I will use ONLY to alert you to news about the book. Info about updates will also be posted here to the book’s blog, of course, and will also appear on the Google+ page and in my normal Twitter stream. But I realized recently that some readers might want to receive specific messages when updates are available. If you purchase the ebook directly from O’Reilly, you’ll get notified through their notification system, but if you purchase through another retailer – or would just like to receive an extra update, please feel free to subscribe. I promise I won’t spam you or do anything else with your email address outside of alert you to the new updates.
Thanks for your interest in the book!
Sep 07
AdhearsionConf 2012 Call For Speakers Ends Tomorrow (Sept 8)
If you answered yes to any of the above questions, why not consider applying to be a speaker? The call for speakers is at:
http://adhearsionconf.com/call-for-speakers/
The only catch is ... the deadline is TOMORROW, Saturday, September 8th!
Ever since I first saw Jay Phillips present about Adhearsion back at one of the early ETel conferences in maybe 2006 or so I've been intrigued by how easy Adhearsion made it to develop telecom apps. It's just incredibly simple to make powerful apps.
If you are a Ruby developer (or want to be) and you are interested in building telephony apps, Adhearsion is definitely worth a look... and if you do use Adhearsion, why not consider signing up as a speaker?
If you found this post interesting or useful, please consider either:
- following me on Twitter;
- adding me to a circle on Google+;
- subscribing to my email newsletter; or
- subscribing to the RSS feed
Sep 07
.NL Becomes First TLD To Pass 1 Million DNSSEC-Signed Domain Names!
History was made today in the ongoing effort to deploy DNSSEC globally and bring about a more secure Internet -
.NL became the first top-level-domain (TLD) to pass 1 million DNSSEC-signed domain names!
Celebrated in tweets from SIDN, the operator of the .NL registry, and from Bert Hubert, principal author of PowerDNS, as well as in an announcement from SIDN, the milestone can be clearly seen in the unofficial .NL statistics site operated by PowerDNS:
It is also visible on SIDN’s home page where they also show the total number of .NL domains:
Note, too, the significance of those numbers –
over 20% of all .NL domains are now signed!
Outstanding to see… and we look forward to seeing how much higher it grows.
We’ve previously covered (also here) the rise of the .NL domain and we’re delighted to see them hit this milestone! Kudos to the folks at SIDN, PowerDNS, SURFnet, NLNet Labs and everyone else involved!
Now we just need to get all the other TLDs moving on the same path! (Including .COM, which has just over 106,000 domains signed… as Bert commented to me on Twitter, .NL had more signed delegations added yesterday than .COM has in total!)
Want to help? Here are some steps for how you can get started signing your domain!
Sep 04
The Amazing Number of Live Video Streams From The Republican And Democratic National Conventions
Naturally, the major US "TV networks" all have their own video livestreams: ABC, CBS, Fox News, CNN. (Interesting to see that NBC was not listed for either convention.) Similarly C-SPAN and PBS will also have livestreams.
This is not really any great surprise since all of those organizations would typically be broadcasting live video coverage from the event anyway over the traditional TV networks, so adding an Internet livestream is really just a matter of putting the technology in place to stream out the existing video feed.
But look at some of the other players...
- The Wall Street Journal is streaming out the DNC convention on both YouTube and through its own mobile apps for iOS and Android (as it did for the RNC convention last week).
- The Sunlight Foundation is streaming out a "fact-checked live stream" (as it did last week for the RNC).
- Politico.com is offering a video livestream tonight as they did last week.
- Various "Occupy" groups have livestreams of the protests at the conventions via Ustream.
... and I'm sure there are probably others who aren't listed on those GigaOm pages who will be streaming out video from the floor of the convention. It's fascinating to look at what tools like YouTube, Google+ Hangouts, Ustream and so many more have done to make it possible for so many more people to offer video livestreams.
Perhaps more importantly, both the Republican and Democratic parties have their OWN video livestreams and in the case of the DNC their own mobile apps.
They are using the Internet to tell their own story in their own words, bypassing the media entirely for those who want to watch the party's view of the event.
So many different players... from both the "traditional" media and so many newer organizations...
Simply amazing at times to see what this Internet thing has enabled... :-)
P.S. And yes, from a technical point of view, I'd be fascinated to learn more about how the various organizations put together the technical capacity to pull this all off. On a network level, there has to be a great amount of bandwidth going into these convention centers... and presumably multiple layers upon layers of redundancy.
Image credit: I took a screenshot of one of the photos on the DNC website.
If you found this post interesting or useful, please consider either:
- following me on Twitter;
- adding me to a circle on Google+;
- subscribing to my email newsletter; or
- subscribing to the RSS feed.
Sep 04
Summer is over… time to get back to IPv6 and DNSSEC – how can we help?
 Here in the northern hemisphere where I live, summer is now basically over. People are (mostly) back from vacations. Kids are returning to school. The rhythms and routines are returning… the weather is getting cooler… the days are getting shorter… people are turning their focus a bit more back to work.
Here in the northern hemisphere where I live, summer is now basically over. People are (mostly) back from vacations. Kids are returning to school. The rhythms and routines are returning… the weather is getting cooler… the days are getting shorter… people are turning their focus a bit more back to work.
Which means it is a perfect time to get back to deploying IPv6 and DNSSEC!
Let’s make it happen now! You’ve still got a few months left to get a project underway in 2012! Or you can be planning for a deployment that will happen in 2013…
Take a look at our IPv6 and DNSSEC resources to see what is out there to help you get started. If you are a website owner, take a look at our “IPv6 for content providers” page that we’ve created… we’re planning to build out the other pages in a similar style for other audiences. If you have a domain name registered, look at our page about how to sign your domain with DNSSEC using various domain name registrars.
If you don’t see a resource that helps you get started, check out our content roadmap to see if what you are looking for is in our plans… and please let us know if you don’t see what you need.
Now is the time to deploy IPv6 and DNSSEC – how can we help?
Sep 03



